- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
Mckinsey 7s Framework Of CyberArk Protecting the Keys to the IT Kingdom
Posted by Matthew Harvey on Feb-11-2020
Introduction
The McKinsey 7s model is a strategic tool and framework that helps managers and businesses assess their performance. The McKinsey 7s model identifies 7 key elements for an organization that need to be focused and aligned for successful change management processes as well as for regular performance enhancements.
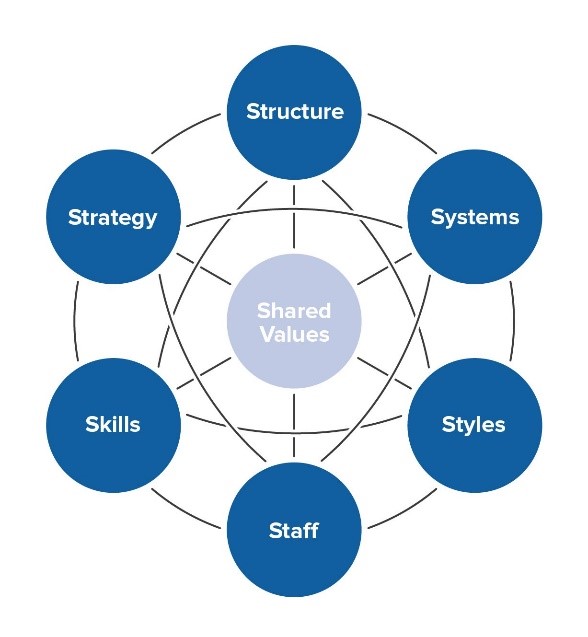
Figure 1 McKinsey 7S Model
The 7 elements identified in the McKinsey 7s model can be categorized as being hard or soft in nature. They are identified as:
| Hard Elements | Soft Elements |
|---|---|
| Shared Values | |
| Strategy | Skills |
| Structure | Style |
| Systems | Staff |
Figure 2 Hard and Soft elements of the McKinsey 7S Model
CyberArk Protecting the Keys to the IT Kingdom makes use of the McKinsey 7s model to regularly enhance its performance, and implement successful change management processes. CyberArk Protecting the Keys to the IT Kingdom focuses on the 7 elements identified in the model to ensure that its performance levels are consistently maintained, and improved for the offerings.
1. Hard elements
The hard elements of the McKinsey 7s model comprise of strategy, structure, and systems. The hard elements of the model are easier to identify, more tangible in nature, and directly controlled and influenced by the leadership and management of the organization.
1.1. Strategy
1.1.1. Clearly defined
The strategic direction and the overall business strategy for CyberArk Protecting the Keys to the IT Kingdom are clearly defined and communicated to all the employees and stakeholders. This helps the organization manage performance, guide actions, and devise different tactics that are aligned with the business strategy. Moreover, the business strategy’s definition and communication also make operations for CyberArk Protecting the Keys to the IT Kingdom more transparent and aligns the responsibilities and actions of the company.
1.1.2. Guiding behaviour for goal attainment
The strategic direction for CyberArk Protecting the Keys to the IT Kingdom is also important in helping the business guide employee, staff, and stakeholder behaviour towards the attainment and achievement of goals. SMART Goals are set with short and long term deadlines in accordance with the business strategy. The business strategy helps employees decide tactics and behaviours for attaining the set goals and targets to help the business grow.
1.1.3. Competitive pressures
CyberArk Protecting the Keys to the IT Kingdom’s strategy also takes into consideration the competitive pressures and activities of competitors. The strategy addresses these competitive pressures through suggestive measures and actions to address competition via strategic tactics and activities that ensure sustainability to CyberArk Protecting the Keys to the IT Kingdom via adapting to market changes, and evolving consumer trends and demands.
1.1.4. Changing consumer demands
An important aspect of the strategy at CyberArk Protecting the Keys to the IT Kingdom is that it takes into constant consideration the changing consumer
trends and demands, as well as the evolving consumer market patterns and consumption behavior. This is an important
part of the strategic direction at CyberArk Protecting the Keys to the IT Kingdom as it allows the company to remain competitive and relevant to its target
consumer groups, as well as allows the company to identify demand gaps in the consumer market.
The company
then strategically addresses these gaps through product offerings and marketing activities which give the company
successful and leading-edge over other patterns in the market.
1.1.5. Flexibility and adaptability
The strategy at CyberArk Protecting the Keys to the IT Kingdom is flexible and adaptable. This is an important aspect of the strategic direction, and strategy setting at CyberArk Protecting the Keys to the IT Kingdom. Rigidity in strategy leads a company and a business to often become stagnant and obstructs advancement, and progression with evolving changes in the consumer markets.
With flexibility and adaptability, the CyberArk Protecting the Keys to the IT Kingdom is not only able to benefit from quickly reacting and responding to changing consumer patterns globally, but is also able to locally and culturally adapt its products via localization for different countries and regions. Moreover, the company is often able to proactively predict consumer market changes, and devise strategic changes accordingly to meet the market trends.
1.2. Structure
1.2.1. Organizational hierarchy
CyberArk Protecting the Keys to the IT Kingdom has a flatter organizational hierarchy that is supported by learning and progressive organizations. With lesser managerial levels in between and more access to the senior management and leadership, the employees feel more secure and confident and also have higher access to information. Moreover, the flatter hierarchy also allows quicker decision-making processes for CyberArk Protecting the Keys to the IT Kingdom and increases organizational commitment in the employees.
1.2.2. Inter-Departmental coordination
CyberArk Protecting the Keys to the IT Kingdom has high coordination between different departments. The company’s departments often form inter-department teams for projects and tasks that require multiple expertise. All coordination between different departments is effective and organized. CyberArk Protecting the Keys to the IT Kingdom has a systematic process for initiating and monitoring coordination between departments to ensure smooth work operations and processes – and goal attainment.
1.2.3. Internal team dynamics [department specific]
CyberArk Protecting the Keys to the IT Kingdom encourages teamwork and team-oriented tasks. Where jobs require individual attention and scope, the company also assigns individual responsibilities and job tasks. However, all employees at CyberArk Protecting the Keys to the IT Kingdom are expected to be team players who can work well with and through other members, and who get along well with other people. The teams at CyberArk Protecting the Keys to the IT Kingdom are supportive of all embers and work in synch with synergy towards achieving the broader team objectives and goals under the CyberArk Protecting the Keys to the IT Kingdom designed strategy and values.
1.2.4. Centralization vs. decentralization
CyberArk Protecting the Keys to the IT Kingdom has a hybrid structure between centralization and decentralization. Like many progressive organizations, CyberArk Protecting the Keys to the IT Kingdom largely supports decentralized decision making. Job roles at CyberArk Protecting the Keys to the IT Kingdom are designed to be carried out with responsibility, and employees often set their goals with mutual coordination and understanding with the supervisors.
However, CyberArk Protecting the Keys to the IT Kingdom is also centralized in making sure that supervisors oversee, and approve of the various efforts, and tactics that employees choose to ensure that they are aligned with the organizational strategy ad values.
1.2.5. Communication
CyberArk Protecting the Keys to the IT Kingdom has a developed and intricate system for ensuring communication between employees, and different managerial levels. The communication systems at CyberArk Protecting the Keys to the IT Kingdom enhance the overall organizational structure. The systematic, defined, and organized communication allows an easy flow of information and ensures that no organizational tasks and goals are compromised because of a lack of communication, or misunderstandings.
1.3. Systems
1.3.1. Organizational systems in place
CyberArk Protecting the Keys to the IT Kingdom has defined and well-demarcated systems in place to ensure that the business operations are managed effectively and that there are no conflicts or disputes. The systems at CyberArk Protecting the Keys to the IT Kingdom are largely departmental in nature, and include, for example:
- Human resource management
- Finance
- Marketing
- Operations
- Sales
- Supply chain management
- Public Relation Management
- Strategic leadership
1.3.2. Defined controls for systems
Each of the defined and demarcated systems at CyberArk Protecting the Keys to the IT Kingdom has especially designed tools and methods as controls for evaluating performance and goal attainment. These controls and measures are designed specifically in different departments based on the nature of their tasks and responsibilities. Moreover, each department also designs specific controls for members for performance evaluation, as well as for inter-departmental tasks and responsibilities.
1.3.3. Monitoring and evaluating controls
CyberArk Protecting the Keys to the IT Kingdom continually evaluates its systems through the designed controls. This monitoring of the performance is continual and ongoing. This is largely done through observation and informal discussions. Feedback to employees and overall department heads is informally given regularly as and when is required. Formal evaluation of performance is also conducted semiannually – or quarterly, depending on the need and the urgency of the projects and assigned tasks. This is a formal process that is undertaken by supervisors and managers to ensure the identification of performance lags, and suggestive means of improvement.
1.3.4. Internal processes for organizational alignment
CyberArk Protecting the Keys to the IT Kingdom also has special processes and methods for ensuring that all departments and systems within the organization are aligned and working in harmony towards the greater business goals and targets. This is made possible through ensuring that all systems are designing and working towards goals and targets specific to their expertise under the broader business vision and strategy. Moreover, the strategic leadership at CyberArk Protecting the Keys to the IT Kingdom also ensures that all systems are allocated with resources, and set specific targets to achieve similar business goals in any specific period.
2. Soft elements
The soft elements of the McKinsey 7s model, in turn, include shared values, staff, skills, and strategy. These elements are less tangible in nature and are more influenced by the organizational culture. As such, the management does not have direct influence or control over them. These elements are also harder to describe and directly identify – but are equally important for an organization’s success and improved performance.
2.1. Shared values
2.1.1. Core values
The core values at CyberArk Protecting the Keys to the IT Kingdom are defined and communicated to foster a creative and supportive organizational structure that will allow employees to perform optimally, and enhance their motivation and organizational commitment. The core values at CyberArk Protecting the Keys to the IT Kingdom include, but are not limited to:
- Creativity
- Honesty
- Transparency
- Accountability
- Trust
- Quality
- Heritage
The CyberArk Protecting the Keys to the IT Kingdom business also ensures that all its activities and operations are conducted with high ethical and moral standards that redefined and benchmarked against international criteria.
2.1.2. Corporate culture
CyberArk Protecting the Keys to the IT Kingdom encourages an inclusive culture that celebrates diversity. The company has an international presence, and production units that are spread across different countries, as such, CyberArk Protecting the Keys to the IT Kingdom ensure that its organizational culture is supportive of diversity, and has internal policies to reduce incidences of discrimination.
The corporate culture at CyberArk Protecting the Keys to the IT Kingdom also encourages innovation and creativity by allowing independence for growth to individuals and teams –thus helping them refine their careers as well as personalities. Lastly, the corporate culture at CyberArk Protecting the Keys to the IT Kingdom also has a supportive leadership which works towards increasing employee motivation and job satisfaction by giving way to visibility and accessibility.
2.1.3. Task alignment with values
CyberArk Protecting the Keys to the IT Kingdom ensures that all its job tasks and roles are aligned with the core values that the company propagates. This means that all activities, tactics, and strategic tactics employed by CyberArk Protecting the Keys to the IT Kingdom will reflect its core values, and will not deviate away from these. This is to ensure a consistent, and reliable brand image, as well as an honest organizational culture. In the event of organizational change, the company will continue to ensure that all change management processes and methods incorporate the core values so that the organizational culture is consistently maintained, and systematically changed if need be.
2.2. Style
2.2.1. Management/leadership style
CyberArk Protecting the Keys to the IT Kingdom has a participative leadership style. Through a participative leadership style, CyberArk Protecting the Keys to the IT Kingdom is able to engage and involve its employees in decision-making processes and managerial decisions. This also allows the leadership to regularly interact with the employees and different managerial groups to identify any potential conflicts for resolution, as well as for feedback regarding strategic tactics and operations. Through its participative leadership, CyberArk Protecting the Keys to the IT Kingdom is able to enhance employee motivation, and increase organizational commitment and ownership amongst employees as well as other stakeholders.
2.2.2. Effectiveness of leadership style
The participative leadership style is highly effective in achieving the business goals and vision of the organization. Employees feel to be active members of the organization who are valued for their suggestions, feedback, and input. Moreover, through participative leadership, leaders and managers are able to identify current and potential conflicts within the CyberArk Protecting the Keys to the IT Kingdom organization, and actively work to resolve them as soon as possible.
2.2.3. Cooperation vs competition – internally
With its supportive and encouraging organizational culture, CyberArk Protecting the Keys to the IT Kingdom gives way to internal collaboration and cooperation between employees, systems, teams, and departments. This cooperation and collaboration at CyberArk Protecting the Keys to the IT Kingdom is important since its operations are spread globally, and also because tasks and responsibilities within the company often require inter-departmental feedback and input. Moreover, with increased expansion, and synergy, the business also regularly forms project teams – which function effectively because of the cooperative and collaborative culture within the CyberArk Protecting the Keys to the IT Kingdom organization.
2.2.4. Team vs groups
CyberArk Protecting the Keys to the IT Kingdom has effective and functional teams and works with them internally to achieve its various business goals and objectives, and complete tasks. The company’s management is encouraging and supportive, and the leadership provides a motivating and pragmatic vision toad achieve. The human resource management system, as well as the organizational training, supports all employees in their growth fairly and transparently. This leads to effective team formation instead of nominal groups within the organization for various projects, as well as department-specific tasks and roles.
2.3. Staff
2.3.1. Employee skill level vs business goals
CyberArk Protecting the Keys to the IT Kingdom has a sufficient number of employees employed across its global operations. Employees for different job roles and positions are hired internally as well as externally – depending on the urgency and the skill levels required. Based on this, it is seen that CyberArk Protecting the Keys to the IT Kingdom has employees who are skilled as per the requirements of their job roles and positions. All employees are given in house training to familiarize themselves with the company and its values. External training along with in-house training is provided for skill level enhancement.
All job roles and positions are designed to facilitate the achievement of business goals, and as such, employee skill level at CyberArk Protecting the Keys to the IT Kingdom is sufficient to achieve the business goals of the company.
2.3.2. Number of employees
CyberArk Protecting the Keys to the IT Kingdom has employed a large number of employees. The number of employees varies from country to country as per the requirements and needs of the business and operations. The global team of CyberArk Protecting the Keys to the IT Kingdom is an inclusive one that accepts, and encourages diversity, and works in synchronization with members to ensure attainment of business goals. The team member sand employees are the most important part of business success for CyberArk Protecting the Keys to the IT Kingdom.
2.3.3. Gaps in required capabilities and capacities
CyberArk Protecting the Keys to the IT Kingdom has a well-defined system for identifying potential needs of capabilities and capacities for the organization. The human resource function of the business has a systematic process that aligns all other departments to identify potential vacancies or skill gaps. Based on the nature of the need, the human resource department arranges for recruitments which may be permanent or contractual in nature, as well as arranges training sessions if need be for the current workforce.
2.4. Skills
2.4.1. Employee skills
CyberArk Protecting the Keys to the IT Kingdom has a commendable workforce, with high skills and capacities. All employees are recruited based on their merit and qualifications. CyberArk Protecting the Keys to the IT Kingdom prides itself on hiring the best professionals and grooming them further to facilitate growth and development.
2.4.2. Employee skills vs task requirements
CyberArk Protecting the Keys to the IT Kingdom has defined tasks and job roles and hires and trains employees for skill levels accordingly with respect to those. The company ensures that all its job requirements are met and that employees have the sufficient skills to perform their respective jobs in accordance with the values and culture as well as the business goals and strategy of CyberArk Protecting the Keys to the IT Kingdom.
2.4.3. Skill management
CyberArk Protecting the Keys to the IT Kingdom pays particular attention to enhancing the skills and capacities of its employees. It arranges regular training and workshops – internally as well as externally managed- to provide growth and development opportunities for its employees. CyberArk Protecting the Keys to the IT Kingdom focuses on personal as well as professional growth for its employees and works accordingly with them.
2.4.4. Company’s competitive advantage
The human resource is one of the core competitive advantages of the company. The skills of employees are developed specifically for job roles and requirements at CyberArk Protecting the Keys to the IT Kingdom and provide a competitive benefit to the company – where players cannot imitate employee skills or training. This creates a unique and non-substitutable competency for CyberArk Protecting the Keys to the IT Kingdom.
3. References
Alam, P.A., 2017. Measuring Organizational Effectiveness through the Performance Management System and Mckinsey's 7 S Model. Asian Journal of Management, 8(4), pp.1280-1286.
Allaoui, S., Bourgault, M. and Pellerin, R., 2019. Business transformation frameworks: Comparison and industrial adaptation. Journal of Enterprise Transformation, pp.1-28.
Arvand, N. and Baroto, M.B., 2016. How to implement strategy more effectively. International Journal of Business Performance Management, 17(3), pp.301-320.
Baishya, B., 2015. McKinsey 7s Framework in corporate planning and policy. International Journal of Interdisciplinary Research in Science Society and Culture (IJIRSSC), 1(1), pp.165-168.
Channon, D.F. and Caldart, A.A., 2015. McKinsey 7S model. Wiley encyclopedia of management, pp.1-1.
Cordell, A. and Thompson, I., 2019. The Procurement Models Handbook. Routledge.
Daft, R., 2016. Contemporary Strategy Analyses. New York: John Wiley & Sons.
Doumi, K., Baina, S. and Baina, K., 2013. STRATEGIC BUSINESS AND IT ALIGNMENT: REPRESENTATION AND EVALUATION. Journal of Theoretical & Applied Information Technology, 47(1).
Galli, B.J., 2018. Change management models: A comparative analysis and concerns. IEEE Engineering Management Review, 46(3), pp.124-132.
Gökdeniz, İ., Kartal, C. and Kömürcü, K., 2017. Strategic assessment based on 7S McKinsey model for a business by using analytic network process (ANP). International Journal of Academic Research in Business and Social Sciences, 7(6), pp.2222-6990.
Grant, R., 2010. Contemporary Strategy Analysis and Cases: Text and Cases. Hoboken: NJ: ohn Wiley & Sons.
Hossain, A., 2019. Strategy implementation: Identification of explanatory variables for successful business analytics implementation in organizations.
Hrebiniak, L., 2005. Making strategy work. Philadelphia, PA: Wharton School Publishing.
Johnson, G., 2016. Exploring strategy: text and cases. Pearson Education.
Král, P. and Králová, V., 2016. Approaches to changing organizational structure: The effect of drivers and communication. Journal of Business Research, 69(11), pp.5169-5174.
Puranam, P. and Vanneste, B., 2016. Corporate strategy: Tools for analysis and decision-making. Cambridge University Press.
Ravanfar, M.M., 2015. Analyzing Organizational Structure based on the 7s model of McKinsey. Global Journal of Management And Business Research.
Shaqrah, A.A., 2018. Analyzing business intelligence systems based on 7S model of McKinsey. International Journal of Business Intelligence Research (IJBIR), 9(1), pp.53-63.
Singh, A., 2013. A study of role of McKinsey's 7S framework in achieving organizational excellence. Organization Development Journal, 31(3), p.39.
Singh, R., 2018. Developing Competitive Strength: Biggest Challenge for the Organizations. Managing Editor, p.65.
Zincir, O. and Tunç, A.Ö., 2017. An Imagination of Organizations in the Future: Rethinking McKinsey's 7S Model. In Strategic Imperatives and Core Competencies in the Era of Robotics and Artificial Intelligence (pp. 101-125). IGI Global.
4. Appendix
| Hard elements |
|
||||||||
| Soft elements |
|
Table 1McKinsey 7S model - summary
Warning! This article is only an example and cannot be used for research or reference purposes. If you need help with something similar, please submit your details here.
Related Articles
- Corporate Social Responsibility of CyberArk Protecting the Keys to the IT Kingdom
- CyberArk Protecting the Keys to the IT Kingdom 5C Marketing Analysis
- The vision statement of CyberArk Protecting the Keys to the IT Kingdom
- Organizational Culture of CyberArk Protecting the Keys to the IT Kingdom
- CyberArk Protecting the Keys to the IT Kingdom Generic and Intensive Growth Strategies
- CyberArk Protecting the Keys to the IT Kingdom Case Study Analysis & Solution
- CyberArk Protecting the Keys to the IT Kingdom Case Solution
- Ansoff Matrix of CyberArk Protecting the Keys to the IT Kingdom
- Blue Ocean Strategy of CyberArk Protecting the Keys to the IT Kingdom
- Hofstede Cultural Model of CyberArk Protecting the Keys to the IT Kingdom
- Porters Diamond Model of CyberArk Protecting the Keys to the IT Kingdom
- Resource Based View Of The Firm - CyberArk Protecting the Keys to the IT Kingdom
- VRIN/VRIO Analysis Of CyberArk Protecting the Keys to the IT Kingdom
- Net Present Value (NPV) Analysis of CyberArk Protecting the Keys to the IT Kingdom
- WACC for CyberArk Protecting the Keys to the IT Kingdom

Massino Simon
5.0

I have excellent grades in Economics. Thank you expert for writing a good term paper.

Vihaan Laban
5.0

Definitely, this service has the goal of eliminating students' anxieties in a way that makes it an exceptional service. Thank you for the deliverance of the paper at the given time.

Kong Wen
5.0

The payment process was very easy and I received more than assumptions. Thank you!

Thomas George
5.0

It’s a great service! Thank you!

Dianna Carl
5.0

These guys did an awesome job for me. On-time delivery and suitable cost. Thank you very much!

Aria Aiden
5.0

Due to my personal experience with this company, I’m going to say that this service has professional writers who deliver papers on time and without an error. Highly recommended!
Next Articles
- 23424-Free-Geek-Toronto-Shaping-a-Social-Enterprise-Mckinsey-7s
- 23425-Massachusetts-Eye-and-Ear-Deciding-Whether-to-Join-Partners-HealthCare-Mckinsey-7s
- 23426-Branding-BY-HEALTH-The-Value-of-Transparency-Mckinsey-7s
- 23427-Becton-Dickinson-Global-Health-Strategy-Mckinsey-7s
- 23428-Tempur-Sealy-International-C-Mckinsey-7s
- 23429-Tempur-Sealy-International-B-Mckinsey-7s
- 23430-Lenovo-Being-on-Top-in-a-Declining-Industry-Mckinsey-7s
- 23431-Driving-Towards-a-Disruption-B-Mckinsey-7s
- 23432-Bicing-Bike-Sharing-in-Barcelona-Mckinsey-7s
- 23433-Actera-Group-Investing-in-Mars-Cinema-Group-A-Mckinsey-7s
Previous Articles
- 1-Making-the-Case-Mckinsey-7s
- 2-Joe-Smith-s-Closing-Analysis-B-Mckinsey-7s
- 3-Joe-Smith-s-Closing-Analysis-A-Spanish-Version-Mckinsey-7s
- 4-GMAC-The-Pipeline-Mckinsey-7s
- 5-On-Writing-Teaching-Notes-Well-Mckinsey-7s
- 6-Exxon-Corp-Trouble-at-Valdez-Mckinsey-7s
- 7-Ashland-Oil-Inc-Trouble-at-Floreffe-A-Mckinsey-7s
- 8-Ashland-Oil-Inc-Trouble-at-Floreffe-B-Mckinsey-7s
- 9-Ashland-Oil-Inc-Trouble-at-Floreffe-C-Mckinsey-7s
- 10-Ashland-Oil-Inc-Trouble-at-Floreffe-D-Mckinsey-7s
Be a Great Writer or Hire a Greater One!
Academic writing has no room for errors and mistakes. If you have BIG dreams to score BIG, think out of the box and hire Essay48 with BIG enough reputation.

Our Guarantees
Interesting Fact
Most recent surveys suggest that around 76 % students try professional academic writing services at least once in their lifetime!







